Encrypting E-mail with GnuPG, Thunderbird and Enigmail
Revision as of 13:44, 20 November 2013 by BobJonkman (talk | contribs) (→Demonstration: Added more steps for demonstration)
On Monday, 2 December 2013 I'm giving a presentation at KWLUG on Encrypting E-mail with GnuPG, Thunderbird and Enigmail which will be followed by a Formal Keysigning.
I'm using this page to develop my presentation notes. If you have comments, criticisms, or suggestions please put them on the Talk page.
--Bob.
I've started to convert this page to presentation slides BobJonkman 19:52, 19 November 2013 (UTC)
Contents
Intro to Crypto
Why use Encrypted E-mail?
- Security
- Your mail cannot be read by a Man In The Middle (MITM)
- Authenticity (Integrity)
- Signed mail cannot be modified in transit, accidentally by mis-configured servers, or maliciously by MITM
- Non-repudiability
- Signed mail can only come from the sender
Why NOT use Encrypted E-mail?
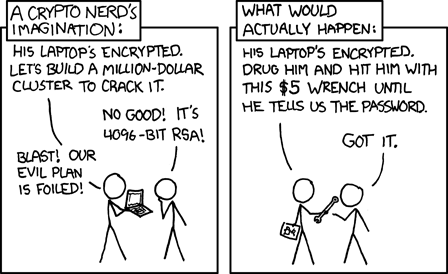
Rubber Hose Cryptography (using a $5 wrench). XKCD
- Need the other party to use the same encryption
- Locked-in format
- Lose your secret key, lose your mail
- Need to keep revoked keys to read old mail
- If your key is compromised, all your old mail is compromised (no forward secrecy)
- Non-repudiability
- Politicians? CEOs?
- Rubber Hose Cryptography (or $5 Wrench Cryptography)
- It's hard!
- and looks geeky...
Crypto Theory
Symmetric Key Encryption
- Substitution cipher, Caesar cipher
- Key = -1
- Encrypt: IBM -1> HAL
- Decrypt: Khmtw Trdq Fqnto +1> Linux User Group
- Key = 13 (ROT13)
- Encrypt: Linux User Group +13> Yvahk Hfre Tebhc
- Decrypt: Yvahk Hfre Tebhc +13> Linux User Group
- Key = -1
- Need a secure way to share key
Public/Private Key Encryption
The Math
- Based on One-way function: Easy to do, hard to reverse
- 59 x 61 = ????
- 59 x 61 = 3599
- 3551 = ?? x ??
- 3551 = 53 x 67
- 59 x 61 = ????
The Practice
- Generate a keypair
- Add e-mail and identity information as you see fit
- Public Key, Private (Secret) Key
- Anything encrypted by one key is decrypted by the other
- Encrypt: Hello World +P> |-|3110 '//0|21|)
- Decrypt: |-|3110 '//0|21|) +S> Hello World
- Encrypt: Linux Is Cool +S> 1!/\/|_|>< !5 (001
- Decrypt: 1!/\/|_|>< !5 (001 +P> Linux Is Cool
- Keep your Secret Key secret!
- But you can distribute your Public Key widely
- Upload your Public Key to keyservers
- Send your Public Key by e-mail
- Use a Public Key to encrypt a message
- Only that person's Secret Key can decrypt it
- You can only encrypt a message to someone whose Public Key you have
- Use your Secret Key to sign (encrypt) a message
- Anyone can use your Public Key to verify (decrypt) the signature, which only you could have created
- You can sign messages for everyone!
- But only people who have your Public Key can verify the signature
- Shows others that encryption is not such a weird thing
- If I download your Public Key, how do I know it's really yours?
- Keysigning!
- You tell me what your Key Fingerprint is.
- I verify that's the same Key Fingerprint on the Public Key I download
- If I believe that's your Public Key, I sign it.
- Web of Trust
- Your Public Key has been signed by others
- I already trust their Public Keys, some of that trust transfers to your Public Key
- Keysigning!
